NoEscape ransomware, discovered in May 2023, represents a significant evolution in the cyber threat landscape as a Ransomware-as-a-Service (RaaS). NoEscape ransomware poses a formidable threat, leveraging advanced features, a shared-profit model, and a focus on customization, showcasing the evolution of cybercriminal tactics in the modern era.
In this comprehensive article, we will explore the NoEscape ransomware variant in detail, and provide information on the indicators of compromise (IOC) associated with the group’s activity.
It’s essential to understand which industries the ransomware targets and have some insight into how it operates to improve your cybersecurity and ransomware defense.
NoEscape ransomware overview
NoEscape ransomware involves a developer offering a platform to affiliates who, in turn, use the ransomware tool on target systems. Affiliates are typically third-party contractors who install and execute NoEscape on behalf of the ransomware operators. It employs a shared-profit model, a common characteristic of contemporary ransomware operations. In this model, the ransom collected is split between the operators and the affiliates.
The developers of NoEscape emphasize a unique approach by claiming that the ransomware is crafted entirely from scratch. This distinguishes it from other ransomware families, as it avoids recycling code from existing malware samples or ransomware products. Building from the ground up enhances its novelty and potentially evades detection mechanisms designed for known code patterns.
NoEscape exhibits flexibility in its choice of targets, relying on the diverse interests and preferences of its affiliates and buyers.
How to identify NoEscape ransomware: Main IOCs
Indicators of compromise (IOCs) are pieces of forensic data that can help identify malicious activity or malware associated with a cyber attack. It includes the encryption extension, file hashes, and IP addresses, among other details cyber criminals leave as they infect a machine or system.
But, if you can’t identify the ransomware strain through its IOCs, you can use Proven Data’s free ransomware ID tool to check if the NoEscape ransomware is the malware that encrypts your files.
Important: Some of these indicators require technical knowledge of the infected system, so you may need to contact your IT team or a digital forensics service provider.
How to handle a NoEscape ransomware attack
It is important to note that handling a ransomware attack can be complex and requires expertise. Therefore, it is recommended to seek professional help from a reputable data recovery service, such as Proven Data to help you recover your data and remove the ransomware from your system.
You can also report the attack to law enforcement agencies, such as the FBI, and cybersecurity organizations to help prevent future attacks and catch the perpetrators.
We strongly recommend contacting cybersecurity services to handle ransomware attacks. Proven Data technicians not only retrieve ransomware-encrypted data but also create forensic reports and streamline incident response, minimizing your business downtime and financial loss.
Important: Do not pay the ransom. Paying the ransom does not guarantee that you will get your data back, and it may encourage the attackers to continue their criminal activities. Check our in-depth article on what happens if you pay the ransom.
How to prevent NoEscape ransomware attacks
Preventing NoEscape ransomware attacks is always the best cybersecurity tactic. If you are a recent victim, you must follow these tips to avoid a new ransomware attack:
Keep your software up to date
Regularly update your operating system and programs to uphold security standards. Reputable OS providers will consistently check their software for vulnerabilities and patch up their security standards to protect against newly detected threats.
Use reputable antivirus software
Employ reputable antivirus software to bolster protection against malware significantly, and regularly check that it is updated. You can also check your network for vulnerabilities and learn where you need to improve your security system.
Be cautious of suspicious emails
Even though there are no known cases of NoEscape using phishing as an attack method, it’s important to exercise caution when dealing with emails from unfamiliar or dubious origins. Refrain from opening files or clicking on links within emails that you are not expecting or seem suspicious.
Do not download cracked software
Cracked software is the term used to describe illicitly modified or pirated versions of commercial software, typically distributed without proper authorization or licensing. Cybercriminals frequently conceal their ransomware executables within cracked software distribution websites, leading users to unwittingly download and execute the malware.
Backup your data
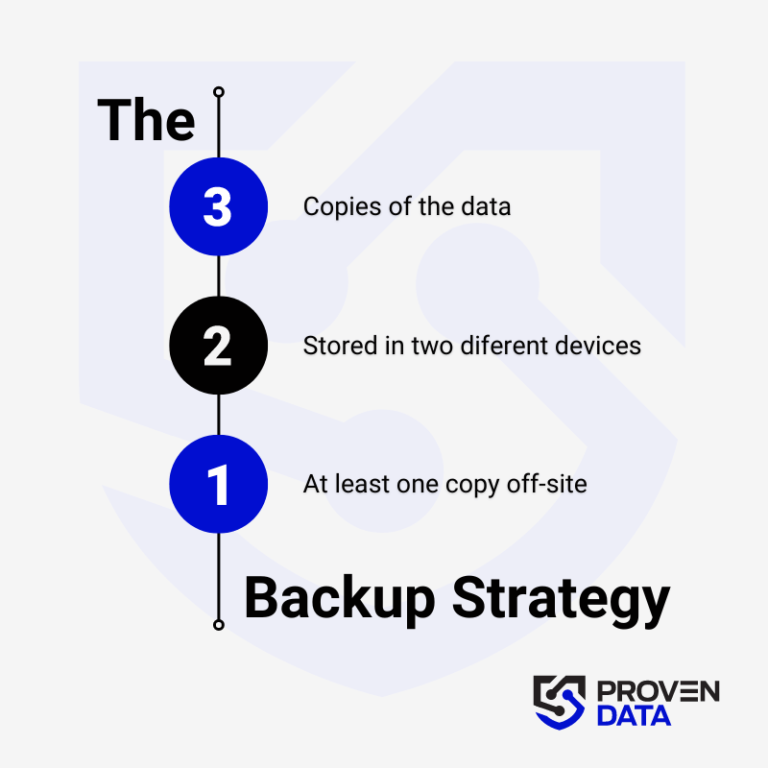
Regularly back up your data to an external hard drive or cloud storage service to prevent complete data loss in case of a ransomware attack. A highly recommended strategy for data loss prevention is the 3-2-1 backup strategy.
The 3-2-1 backup strategy involves creating three total copies of your data: two on different media and one offsite, ensuring redundancy and protection against data loss. And at least one copy offsite to prevent loss due to natural disasters or other local incidents.
Educate yourself and your teams
Educate yourself and your employees about the risks of ransomware and how to avoid it, such as avoiding suspicious emails or downloads.
Consult cybersecurity professionals
Proven Data offers cyber security services to help you keep your data protected against threat actors. From vulnerability assessment to ensure your systems and servers do not have open doors for cyber attacks, to Incident Response (IR) services for immediate response in case of a successful attack.
We also have the option of managed detection and response (MDR) services that help organizations improve their security posture, minimize risk, and protect sensitive data and assets.